.png)
.png)
Most business owners assume their technology is “fine.” The internet works. Emails send. Phones ring. And because everything appears to function day-to-day, technology rarely becomes a priority — until something breaks.
But in reality, technology failures are rarely sudden. They are usually the result of gradual misalignment between how a business operates today and how its systems were originally set up.
As businesses grow, systems are layered on. New tools are introduced. Staff numbers increase. Yet the underlying structure is rarely revisited.
According to the Australian Cyber Security Centre (ACSC), small and medium businesses remain one of the most targeted
segments for cyber incidents, largely due to gaps in visibility and outdated systems rather than deliberate neglect.
At the same time, research from Deloitte and SMB Digital Transformation studies consistently shows that SMEs underutilise
between 30–50% of the technology they already pay for, particularly in platforms like Microsoft 365.
For businesses with 10–100 staff, particularly in sectors such as childcare, legal, medical and professional services —
where systems are relied upon every day — this quiet drift creates hidden risks, inefficiencies and unnecessary costs.
At ZaheZone, when we step back and review a business’s technology environment, four areas almost always reveal opportunities for
improvement.
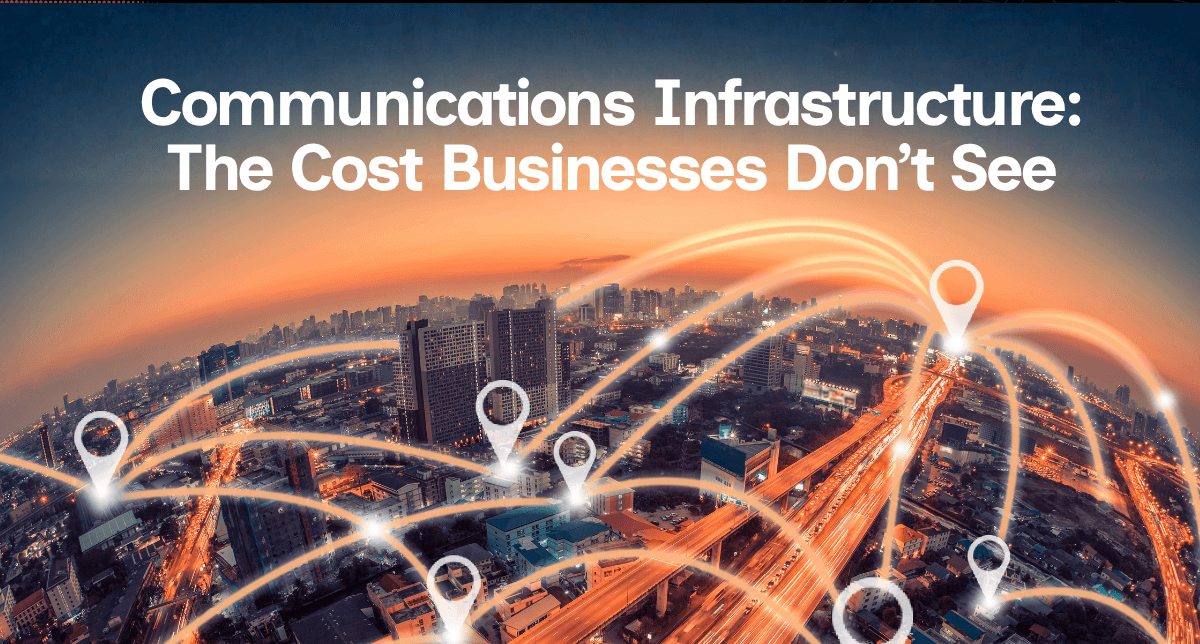
Communication systems tend to evolve reactively rather than strategically.
A new internet connection is installed to solve a speed issue. Mobile plans are added as staff numbers grow. Phone systems are
introduced or patched into existing setups.
Over time, what emerges is a system that works — but not necessarily one that is optimised.
Common patterns we see include:
• Multiple providers with overlapping services
• Mobile plans that no longer match usage
• Hardware-heavy setups creating unnecessary replacement costs
• Limited visibility or accountability across devices
A practical example we encountered involved a business spending over $17,000 per year replacing lost company-issued phones —
not due to misuse, but simply due to lack of accountability structures.
By shifting to a secure communication platform on personal devices, the business reduced costs significantly while improving flexibility and control.
These are not complex transformations — they are structural adjustments that align technology with how the business actually operates.
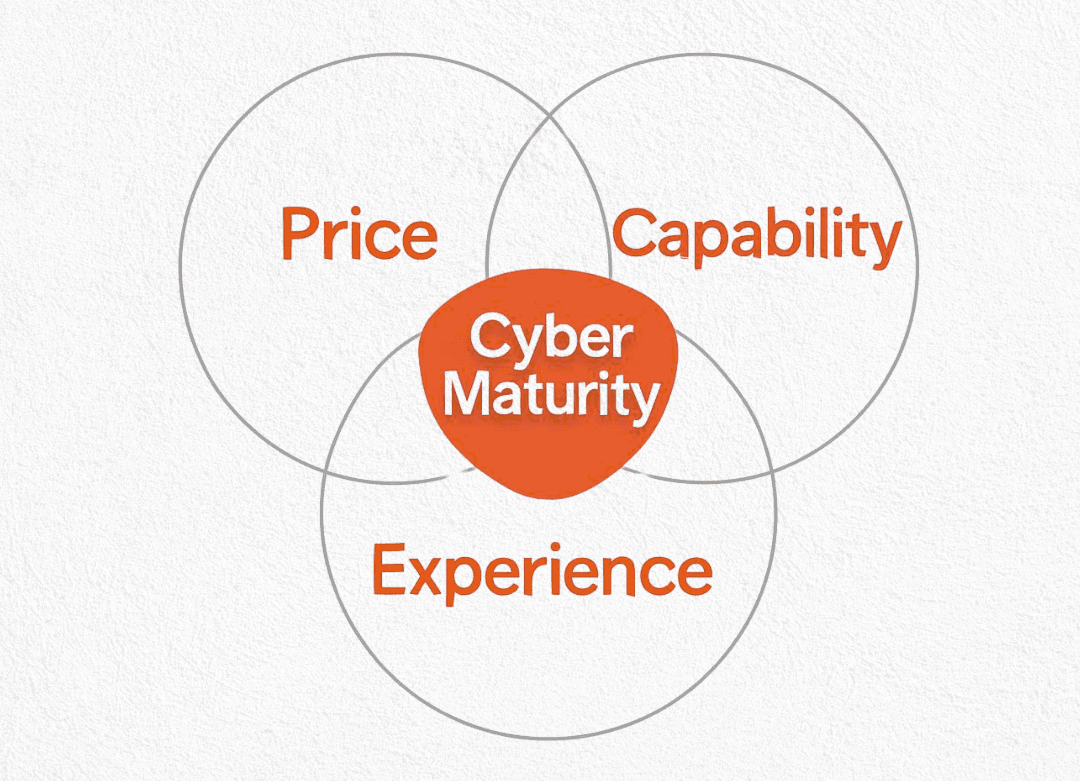
Cyber security is no longer just a technical conversation — it is now a commercial requirement.
Increasingly, insurers, banks and enterprise clients are asking:
“Can you demonstrate your cyber security standards?”
The ACSC Annual Cyber Threat Report highlights that the average cost of cyber incidents for small businesses continues to rise, while many breaches still occur due to basic gaps such as:
• Weak or inconsistent password policies
• Lack of multi-factor authentication
• Incomplete backup strategies
• Unmonitored endpoints and devices
Many businesses believe they are “secure enough,” yet when reviewed, security settings across email systems, devices and networks are often incomplete or inconsistent.
Frameworks such as SMB1001 are emerging to help small and medium businesses align with global standards, providing a structured and practical approach to cyber security.
The objective is not to introduce complexity — it is to ensure that fundamental protections are in place before a problem occurs. Read more about SMB1001 in our recent article here.
Microsoft 365 has evolved far beyond email and document storage. It is now a comprehensive platform that integrates:
• Security and compliance tools
• Collaboration and communication systems
• Workflow automation and productivity features
However, research from Microsoft and independent digital adoption studies indicates that most businesses only utilise a fraction of these capabilities.
In practice, we regularly see:
• Security features that have never been activated
• Multi-factor authentication only partially implemented
• Teams unaware of tools already included in their licences
• Businesses overpaying for licences that don’t match actual usage
This creates a paradox — businesses invest in technology but fail to extract its full value.
A structured review often results in:
• Improved security posture
• Increased team productivity
• Reduced licensing costs
Without the need for additional investment.
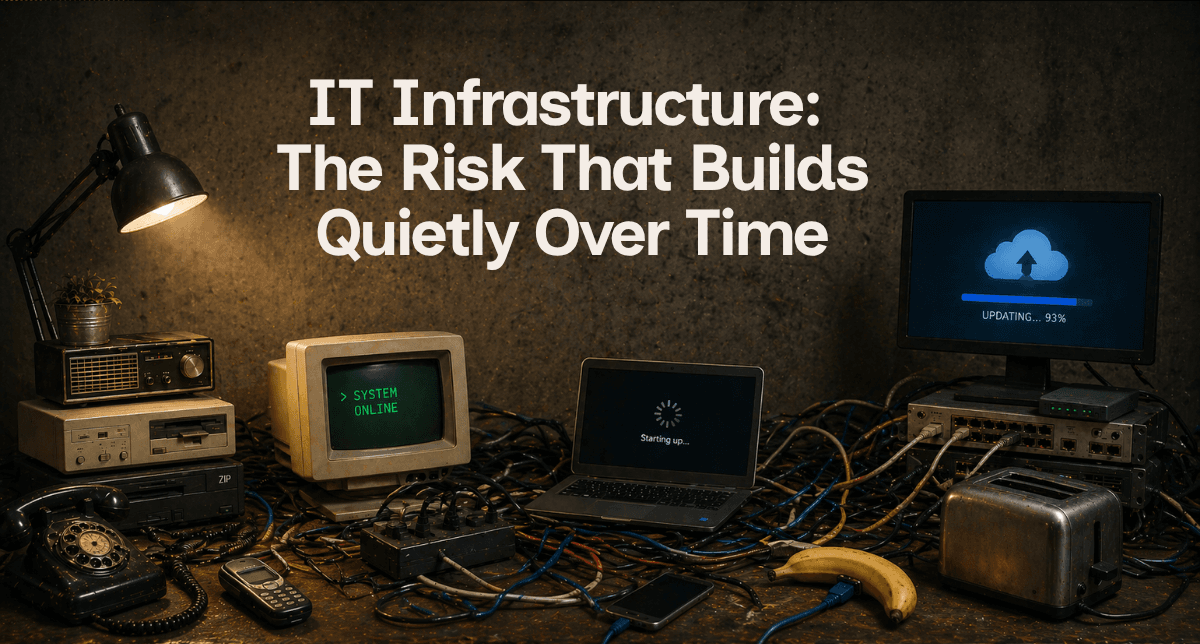
Technology environments rarely start complex — they become complex over time.
New devices are added.
Software layers accumulate.
Networks expand organically.
Without a cohesive strategy, the infrastructure becomes fragmented.
Common risks include:
• Ageing or unsupported hardware
• Incomplete or untested backup systems
• Software no longer receiving updates
• Inconsistent security configurations
Individually, these issues may seem minor. Collectively, they introduce fragility into the business.
According to IBM’s Cost of a Data Breach Report, system complexity and lack of visibility are among the leading contributors to downtime and recovery costs.
And when failure occurs, it is rarely convenient — it impacts operations, revenue and client trust simultaneously.
The Goal Is Not Complexity — It’s Clarity
Most business owners are not avoiding technology reviews — they are prioritising their business. The role of a technology review is not to overwhelm with jargon or unnecessary upgrades.
It is to provide clarity:
• Where are the risks?
• Where are the inefficiencies?
• What improvements will have the greatest impact?
Often, the outcome is not a major overhaul — but a series of practical recommendations that strengthen the business as a whole.
ZaheZone’s Technology Health Checks are designed to provide a clear, practical snapshot of a business’s technology environment.
These reviews typically assess:
• Communications systems
• Cyber security posture (SMB1001 aligned)
• Microsoft 365 configuration and licensing
• Overall IT infrastructure
The objective is simple:
Improve reliability, reduce risk, and ensure technology is aligned with how the business operates today — not how it operated years ago.
References

Being ‘secure enough’ is no longer enough. SMB1001 gives South East Queensland businesses a practical, tiered path to proving cyber maturity, reducing insurance risk, unlocking contracts, and building trust. This article explains why SMB1001 is fast becoming the new standard for growth-focused SMBs — and how to approach compliance as a business investment, not an IT cost
.jpg)
Think cyber security tools keep your business safe? Real protection requires configuration, monitoring, and leadership oversight. Read the full article to understand the risks and how to close the gaps.







.png)



At ZaheZone, we take your business growth seriously, which is why we’re with you every step of the way. To discover how we can help you optimize and scale your IT, contact us today.